You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
In this document we're going to show you step by step what you have to do to set your own VCI demo up.
21
+
In this document we're going to show you step by step what you have to do to setup your own VCI demo.
18
22
19
-
The demo consists of 3 components, which can be found in the packages folder.
23
+
The demo consists of 2 components, which can be found in the packages folder.
20
24
21
25
- The agent using our [SSI-SDK](https://github.com/Sphereon-OpenSource/SSI-SDK), responsible for key-management, DIDs,
22
26
Presentation Exchange storage, Issuer Metadata Storage, as well as
23
27
actual issuance and verification of Credentials. It can handle multiple issuer configurations as well as
24
28
Verifiers/Presentation definitions at the same time, although the frontends only will use one
25
-
- A Demo Issuer frontend, allowing you to fill out a simple form, or using a wallet, to supply some information, which
26
-
then will be used to issue a credential containing that information. This code can be exported and run on a regular
29
+
- A Demo frontend, allowing you to fill out simple form(s), or using a wallet, to supply some information, which
30
+
then will be used to issue a credential containing that information. The screens are configurable and you can create
31
+
your own sequences. You can also change the look and feel and thus apply branding. This code can be exported and run
32
+
on a regular
27
33
webserver if you want. It is a frontend communicating with the agent, using some of our OID4VC SSI-SDK plugins.
28
-
- A Demo Verifier frontend, allowing you to verify the Credential issued by the agent (the demo issuer, also contains
29
-
similar functionality if you would follow the wallet flow btw). Be aware that we will replace this demo frontend with
30
-
something a bit more appealing soon.
31
34
32
35
The Demo is using code from our [SSI-SDK](https://github.com/Sphereon-OpenSource/SSI-SDK), providing 11 modules for
33
36
OID4VC, QR code generation, as well as Issuance branding. Integrating these technologies with a Key Management System,
@@ -45,20 +48,24 @@ The most prominent low-level libraries are:
45
48
## Wallet Prerequisites
46
49
47
50
You will need an OID4VC capable wallet, that supports SIOPv2, OID4VP, OID4VCI and Presentation Exchange. You can use our
48
-
Open-Source wallet from the stores. You can see our [Wallet demo instructions](https://sphereon.com/sphereon-products/sphereon-wallet/sphereon-wallet-demo-instructions/)
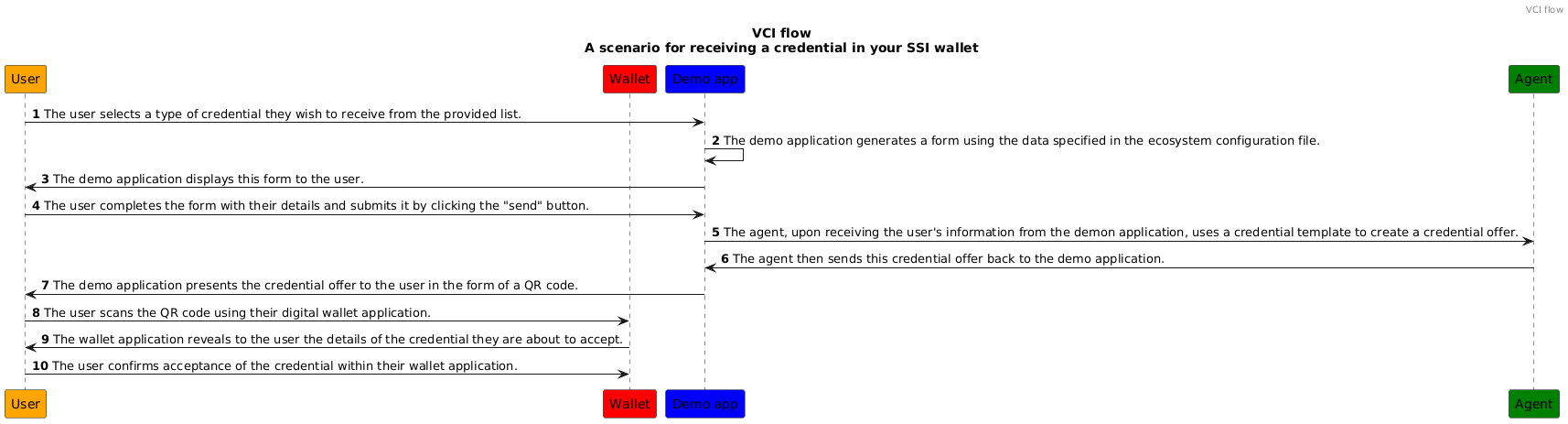
A scenario for fetching a credential. Note that since the process is dynamic, your setup might be a little different, but the main parts will stay the same.
58
+
A scenario for fetching a credential. Note that since the process is dynamic, your setup might be a little different,
59
+
but the main parts will stay the same.
54
60
55
-
//TODO: when merged, change the address
56
-

61
+
57
62
58
63
And a scenario for using Verifiable Credential(s) For OID4VP flow:
In the next chapters we're going to show you how to setup the `agent` module, oid4vci-demo-front-end and a brief introduction on how credential branding actually works.
66
+
# Step by Step instructions
67
+
In the next chapters we're going to show you how to setup the `agent` module, oid4vci-demo-front-end and a brief
68
+
introduction on how credential branding actually works.
62
69
63
70
-[Setting up the agent](./documents/agent-setup.md)
64
71
-[Setting up VCI frontend](./documents/vci-front-end.md)
@@ -73,15 +80,21 @@ docker-compose build
73
80
docker-compose up
74
81
```
75
82
76
-
The build phase might take a few minutes. If you run the docker-compose up command 3 services will be running. The ssi-agent, oid4vci-demo-frontend and oid4vp-frontend.
83
+
The build phase might take a few minutes. If you run the docker-compose up command 3 services will be running. The
84
+
ssi-agent, oid4vci-demo-frontend and oid4vp-frontend.
77
85
78
-
You should now be able to go to http://host.docker.internal:5001 and http://host.docker.internal:5002 respectively to test the issuer and verifier demo's.
86
+
You should now be able to go to http://host.docker.internal:5001 and http://host.docker.internal:5002 respectively to
87
+
test the issuer and verifier demo's.
79
88
80
-
Please note that you might have to configure your docker environment to expose the host.docker.internal like the image below. If you cannot make that work you could adjust the config/docker and docker/*.env files to suit your needs
89
+
Please note that you might have to configure your docker environment to expose the host.docker.internal like the image
90
+
below. If you cannot make that work you could adjust the config/docker and docker/*.env files to suit your needs
#### Environment variables and configuration for docker.
85
-
Please note that the environment variables for the 3 images come from the ./docker folder. You will have to copy the 3 example files and remove the .example suffix.
86
95
87
-
The configuration files are copied over to the agent image. So the above explained configuration options also apply when running in docker.
96
+
Please note that the environment variables for the 3 images come from the ./docker folder. You will have to copy the 3
97
+
example files and remove the .example suffix.
98
+
99
+
The configuration files are copied over to the agent image. So the above explained configuration options also apply when
Copy file name to clipboardExpand all lines: documents/credential-branding.md
+6-1Lines changed: 6 additions & 1 deletion
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -19,6 +19,11 @@
19
19
20
20
Credential branding is an essential aspect of Verifiable Credentials (VCs) that helps define how a credential is displayed and identified to end-users. It plays a crucial role in creating a user-friendly and consistent experience for individuals who interact with verifiable credentials. In this explanation, we give you a detailed account of the concept of credential branding as defined in the [Verifiable Credentials Issuance (VCI) spec](https://openid.net/specs/openid-4-verifiable-credential-issuance-1_0.html) specification.
21
21
22
+
An example of a branded credential in the Sphereon wallet:
In the context of VCs, "Credential Branding" refers to the visual and descriptive attributes associated with a credential, including its name, logo, background color, and more. These attributes are defined in the metadata of the credential issuer and are used to present the credential in a consistent and nice way to the credential holder or verifier.
@@ -86,4 +91,4 @@ Beyond names and claim labels, other optional branding elements can be locale-ad
86
91
-`description`: Offer a localized description of the credential.
87
92
-`background_color` and `text_color`: Set locale-specific colors for the credential's background and text, ensuring that the visual presentation aligns with the language and regional norms.
88
93
89
-
By utilizing these customizable display options, you can enhance the user experience with a display that is both visually and linguistically tailored to requirements of your user. Read more details in the [OID4VCI specification](https://openid.net/specs/openid-4-verifiable-credential-issuance-1_0.html#section-10.2.3.1-2.5.1).
94
+
By utilizing these customizable display options, you can enhance the user experience with a display that is both visually and linguistically tailored to requirements of your user. Read more details in the [OID4VCI specification](https://openid.net/specs/openid-4-verifiable-credential-issuance-1_0.html#section-10.2.3.1-2.5.1).
0 commit comments